🎧 Related Podcast Episode
Executive Summary
The landscape of cybersecurity compliance is undergoing a fundamental transformation as organizations move into 2026. Rapid advances in Artificial Intelligence (AI) are simultaneously empowering threat actors and providing organizations with the tools to automate up to 50% of compliance workloads. The focus of regulatory bodies and insurers has shifted from “proof of backup” to “proof of recoverability,” with a heightened emphasis on continuous monitoring over periodic auditing. Strategic leaders are now required to navigate a complex environment defined by increasing ransomware severity—noted by a 95% increase in global average payment amounts in 2025—and a tightening insurance market that demands rigorous evidence of control effectiveness.
The Role of AI in Compliance Automation
AI-powered platforms have reshaped SOC 2 and other framework evidence collection by replacing manual, repetitive tasks with automated, API-driven workflows.
Efficiency Gains and Cost Metrics
Traditional audit preparation is resource-intensive, often disrupting daily operations. AI automation offers a significant reduction in both time and financial expenditure.
|
Metric |
Traditional Compliance |
AI-Powered Compliance | |
Preparation Time |
300–500 hours |
110–170 hours | |
Direct Costs |
50,000–100,000+ (Consultants) |
5,000–25,000 (Software) | |
Monitoring Frequency |
Periodic / Point-in-time |
Continuous / 24/7 | |
Evidence Collection |
Manual screenshots/spreadsheets |
Automated API-driven collection | |
Audit Readiness |
Periodic scramble |
Always audit-ready |
Technical Capabilities of AI Automation
- Automated Evidence Collection: AI platforms connect directly to tech stacks (AWS, Azure, Okta, GitHub, Workday) via APIs to pull configuration data and logs. For legacy systems lacking APIs, advanced AI agents can capture security settings manually.
- Continuous Monitoring: Unlike traditional audits that capture snapshots, AI systems monitor environments 24/7. They immediately flag issues such as unencrypted S3 buckets or disabled multi-factor authentication (MFA).
- Intelligent Control Mapping: A single piece of evidence (e.g., an MFA log) can be automatically mapped across multiple frameworks, including SOC 2, ISO 27001, and HIPAA, reducing redundant efforts.
- Validation and Accuracy: Machine learning algorithms check documentation against test criteria to ensure integrity, reducing the 98% exception rate typically found in manual SOC 2 Type 2 reports.
Understanding Auditing Standards: SSAE 18 and SSAE 21
Compliance reports are governed by specific standards established by the AICPA, which have evolved to address increasing system complexities.
SSAE 18 (Statement on Standards for Attestation Engagements No. 18)
Issued in 2017 to replace SSAE 16, SSAE 18 is the auditing standard that governs how SOC examinations are performed.
- Key Requirements: It strengthened reporting requirements for risk management, internal control monitoring, and the oversight of subservice organizations (vendors).
- Management Assertion: Requires the service organization to provide a signed assertion regarding the fairness and suitability of their control descriptions.
SSAE 21 and Direct Examination
SSAE 21, effective for reports dated on or after June 15, 2022, introduced “Direct Examination Engagements” (AT-C section 206).
- Practitioner Role: It enables auditors to measure or evaluate underlying subject matter against criteria and express an opinion directly.
- Key Shift: In a direct examination, the responsible party is not required to provide a written assertion, and the practitioner is not required to obtain one. This differentiates it from “Assertion-Based Examination Engagements” (AT-C section 205).
SOC 2 Framework and Trust Services Criteria (TSC)
SOC 2 reports evaluate controls based on five key criteria:
- Security: (Mandatory) Protection against unauthorized access.
- Availability: Ensuring systems are operational as promised (uptime, disaster recovery).
- Processing Integrity: Confirming data is processed accurately and completely.
- Confidentiality: Protecting sensitive business data from unauthorized disclosure.
- Privacy: Handling personal data (PII) according to proper collection and retention practices.
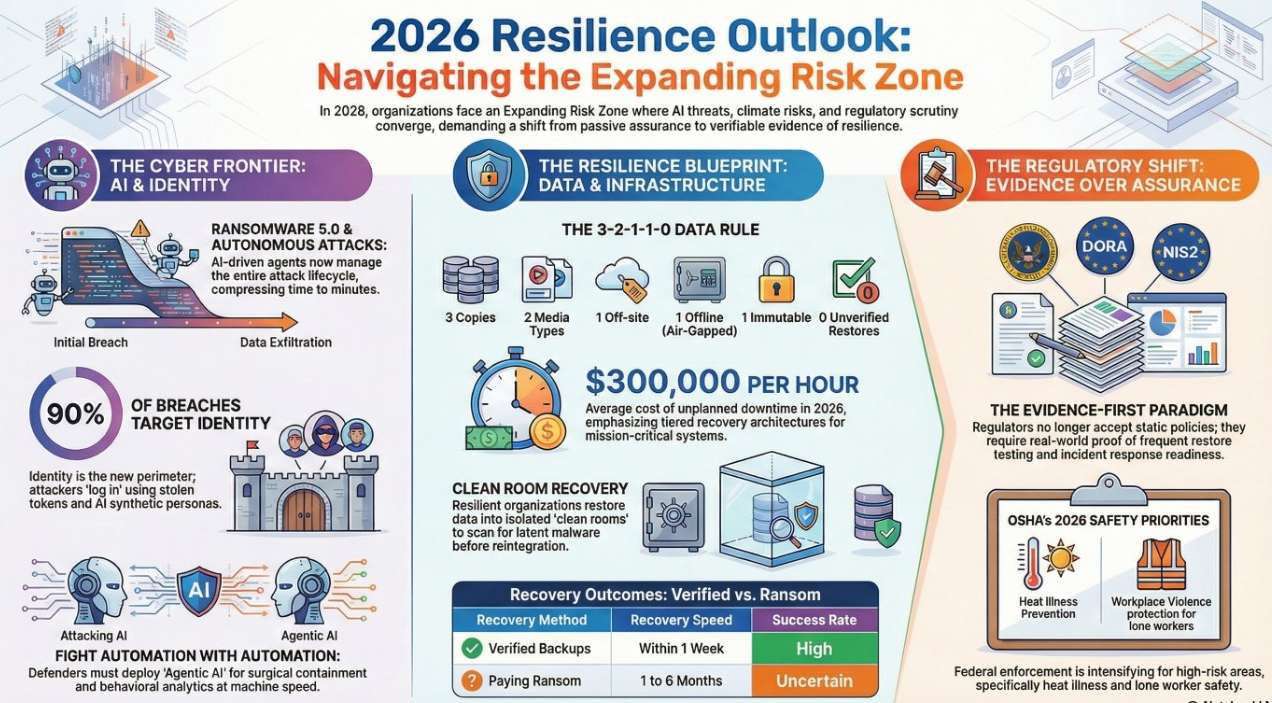
The 2026 Cyber Threat Environment
The risk environment has escalated into a “board-level priority” due to AI-driven threats and systemic vulnerabilities.
AI-Driven Asymmetrical Warfare
Threat actors are using AI to scale and automate attacks with unprecedented speed.
- Autonomous AI Attacks: Machine agents independently coordinate multi-stage campaigns.
- Adaptive Malware: Malicious code that evolves to bypass traditional detection.
- Synthetic Insider Threats: Mimicking real users using stolen data and voice samples to infiltrate platforms.
Ransomware and Systemic Risk
- Ransomware Resurgence: Global ransomware claims increased by 74% in 2025, while payment amounts nearly doubled.
- Supply Chain Vulnerabilities: Third-party involvement accounted for 30% of all data breaches in 2024. Systemic incidents (e.g., CrowdStrike) demonstrate how single points of failure in the third-party ecosystem can lead to catastrophic losses across multiple businesses.
Strategic Resilience and Disaster Recovery
By 2026, regulatory and insurance pressures are forcing a shift from defensive-only strategies to “secure by design” resilience.
Regulatory Drivers (CSRB, NIS2, DORA)
- DORA and NIS2: These EU-led regulations (with global reach via supply chain pressure) demand that organizations prove recoverability, not just backup status.
- CSRB (UK): Reshapes what “good” looks like for IT teams, requiring evidence-backed assurance.
- SEC Rules: In the U.S., new disclosure rules require cyber incidents to be reported within four days.
Proving Recoverability
The “uncomfortable truth” for many organizations is the inability to prove end-to-end recoverability in ransomware or insider threat scenarios.
- Immutable Backups: True immutability must protect backup infrastructure and admin credentials, as these are primary targets for ransomware.
- Verified Recovery Workflows: Organizations must move toward automated verification and “clean room” recovery environments to prevent contaminated data from being restored into production.
- Resilience as a KPI: Organizations are increasingly tracking and reporting resilience metrics as a formal business objective to satisfy insurers and stakeholders.
Synergy of AI Automation and Human Oversight
While AI handles data gathering and anomaly detection, human judgment remains essential for high-stakes decision-making.
The Human-in-the-Loop Model
|
Feature |
AI Role in Evidence Collection |
Human Role in Oversight | |
Scoping |
Mapping systems to controls |
Defining significance and audit scope | |
Data Gathering |
Extracting logs and screenshots |
Ensuring completeness and context | |
Control Testing |
Validating against set parameters |
Applying judgment to exceptions | |
Decision Making |
Flagging patterns/anomalies |
Interpreting alerts; strategic remediation | |
Accountability |
Maintaining audit trails |
Approving management assertions |
Governance Controls
Organizations must designate “control owners” responsible for verifying AI outputs. Humans are required to interpret nuanced business contexts—such as whether a specific control is audit-relevant—that machine learning models cannot yet fully grasp.
Industry-Specific Insights
Healthcare Organizations
Healthcare entities face unique challenges due to Protected Health Information (PHI) and complex medical device ecosystems.
- Risk: The average cost of a data breach in healthcare reached $10.93 million.
- Automation Benefit: AI automates vendor risk management by ensuring Business Associate Agreements (BAAs) are in place before any data exposure occurs.
Startups and Early-Stage Companies
For pre-revenue startups, automated SOC 2 compliance is a strategic advantage for enterprise sales. It allows them to demonstrate security maturity without building an extensive internal security team, reducing the time-to-audit-ready status to 4–8 weeks.
Conclusion and Strategic Action Items
Organizations must treat 2026 as a strategic planning window rather than a distant horizon. To remain compliant and resilient, leaders should:
- Reinvest premium savings from favorable insurance markets into strengthening core cyber defenses.
- Transition from manual snapshots to 24/7 AI-driven continuous monitoring.
- Establish clear accountability frameworks that combine AI efficiency with rigorous human oversight.
- Prioritize “proof of recoverability” by testing disaster recovery workflows in immutable, clean environments.